Which permissions does Codacy need from my account?#
Codacy Cloud uses the OAuth protocol to handle logins and supports the following providers:
Codacy requests only the necessary permissions from your Git provider to analyze your code and keeps your information secure. See the sections below for the detailed list of permissions that Codacy asks for depending on the provider.
GitHub Cloud#
If you log in with GitHub, Codacy requires the following app permissions:
| Scope | Permissions | Description |
|---|---|---|
| Repository permissions: | ||
| Checks | Read & Write | Codacy creates and updates check runs with the results of code analysis. |
| Issues | Read & Write | Codacy can create GitHub issues from issues found during code analysis. |
| Metadata | Read-Only | Codacy retrieves repository metadata, such as name, languages, collaborators and commit information. |
| Pull requests | Read & Write | Codacy retrieves pull request information to display on its side. Codacy might also create comments and suggestions on the pull request, according to the results of code analysis. |
| Webhooks | Read & Write | Codacy creates webhooks for code pushes and pull request events (created, merged, etc.). These events might trigger code analysis. |
| Commit statuses | Read & Write | Codacy sets the status of commits according to the result of code analysis. |
| Contents | Read-Only | Codacy retrieves repository contents to get installation access tokens when integrating with your repositories and clone them, and for code coverage analysis. Codacy requests this permission since September 2023. Make sure an organization owner approves Codacy GitHub App updated permissions on your GitHub organization. |
| Merge groups | Read-Only | Codacy listens for the `merge_group` webhook event and responds to the `checks_requested` action accordingly. |
| Organization permissions: | ||
| Webhooks | Read & Write | Codacy creates webhooks for organization and repository events (creation, deletion, member added, etc.). |
| Members | Read-Only | Codacy retrieves information about organization members and teams to enforce permissions and user management. |
User permissions: These permissions are granted on an individual user basis as part of the user authorization flow. They will be also be displayed during account installation for transparency. |
||
| Email addresses | Read-Only | Codacy retrieves the user's email addresses to enforce which commits are eligible for analysis. |
GitLab Cloud#
If you sign up with GitLab Cloud, Codacy requires the following permissions/scopes:
| Scope | Description |
|---|---|
api |
Codacy uses GitLab's API to read and update pull requests, create webhooks for code push events, list commits, repositories, groups, members and permissions. |
read_user |
Codacy retrieves the user's email addresses to enforce which commits are eligible for analysis. |
read_repository |
Codacy retrieves repository metadata, such as name, languages and collaborators. |
openid |
Codacy uses this permission for authentication using OpenID Connect. |
Bitbucket Cloud#
If you log in with Bitbucket, Codacy requires the following permissions/scopes:
| Scope and permissions | Description |
|---|---|
account:write |
Codacy retrieves the user's email addresses to enforce which commits are eligible for analysis. |
repository:admin |
Codacy retrieves repository metadata, such as name, languages and collaborators, and commit information. Codacy creates an SSH key on the repository to allow cloning and integrating with your repository. |
pullrequest:write |
Codacy retrieves pull request information to display on its side. Codacy might also create comments on the pull request, according to the results of code analysis. |
issue:write |
Codacy can create Bitbucket issues from issues found during code analysis. |
webhook |
Codacy creates webhooks for code pushes and pull request events (created, merged, etc.). These events might trigger code analysis. |
team |
Codacy uses your group/team membership information to enforce permissions. |
| Read your workspace's project settings and read repositories contained within your workspace's projects. |
Revoking access to integrations#
To revoke the access from Codacy to one or more of the OAuth providers:
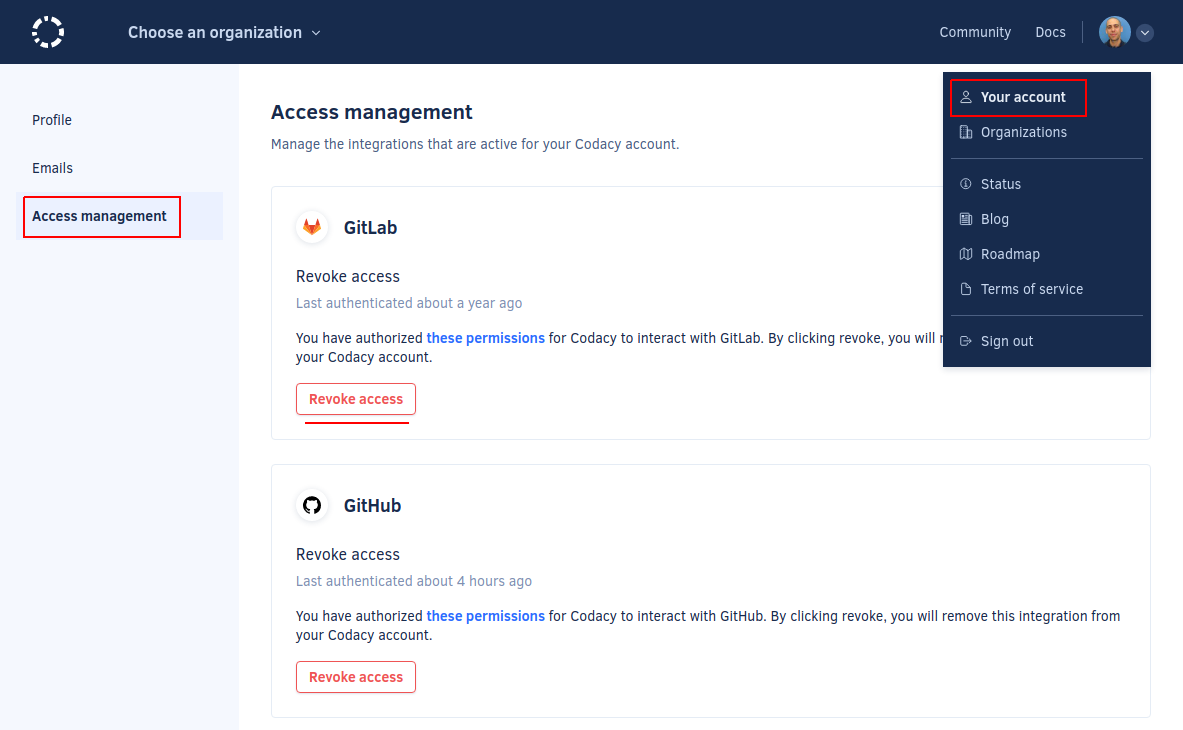
- Click on your avatar on the top right-hand corner and select Your Account, tab Access Management.
-
The Access Management page lists all current integrations with Git providers that you used to sign in or log in to Codacy. To revoke access to an integration, click the button Revoke access for the intended integration.
-
To ensure that the integration is removed not only on Codacy but also on the integration side, it's important that you revoke the Codacy OAuth application access on your provider:
After revoking an integration, Codacy will no longer be able to access or manipulate resources that require API calls, such as detecting new pull requests or adding comments to pull requests. However, Codacy will still be able to perform operations that only require using the Git protocol either via SSH or HTTPS, such as detecting new commits and calculating diffs. To remove your repositories from Codacy and stop the analysis you must delete them from your Codacy account.
If you need to use an integration that you have previously revoked, log in again to Codacy with that integration so that Codacy can request the required permissions from the provider.
Why does Codacy ask for permission to create SSH keys?#
This section applies only to GitLab and Bitbucket
On GitLab and Bitbucket organizations, when you add a private repository to Codacy, Codacy uses the integration with your Git provider to create a new SSH key on the repository. Codacy then uses that SSH key every time it needs to clone the repository.
Codacy only adds read-only SSH keys and can't access any of your existing SSH keys. You have full control over which organizations and repositories Codacy is authorized to access. Codacy doesn't change the contents or member privileges of any repository you authorize it to analyze.
We understand the desire for security and privacy and find that the SSH protocol is preferable to HTTPS as it separates Codacy's access rights from the one of the users.
Tip
You can revoke the keys created by Codacy at any time. See GitLab or Bitbucket documentation for further details.
Share your feedback 📢
Did this page help you?
Thanks for the feedback! Is there anything else you'd like to tell us about this page?
255 characters left
We're sorry to hear that. Please let us know what we can improve:
255 characters left
Alternatively, you can create a more detailed issue on our GitHub repository.
Thanks for helping improve the Codacy documentation.
Edit this page on GitHub if you notice something wrong or missing.
If you have a question or need help please contact support@codacy.com.